This article discusses how scam cases in Singapore increased by 16% from 2020 to 2021, with the total amount cheated rising from S$63.5 million to S$168 million in that period. It highlights three significant types of scams:
- Bank-related phishing scams: Victims receive fake SMSes claiming issues with their banking accounts and are redirected to fraudulent websites where they enter their login details.
- Tech support scams: Scammers impersonate technical support staff, claiming the victim’s internet router is compromised. They convince victims to install remote access software like TeamViewer, giving scammers control over their computers and access to bank accounts.
- Investment scams: Fraudsters pose as stockbrokers or financial employees on social media, convincing victims to transfer money to overseas banks for supposed fees and taxes related to investments.

The article also provides prevention tips from the Monetary Authority of Singapore:
- Don’t click links in SMSes or emails
- Never share banking credentials or passwords
- Verify communications by calling your bank directly
- Check that you’re on the official bank website before transactions
- Monitor transaction notifications closely

Additionally, the article offers specific safety measures for DBS/POSB customers regarding updating personal information, enabling transaction notifications, setting up digital tokens, and controlling transaction limits.
Analysis of Scams in Singapore
Common Patterns in the Scams
Looking at the three significant scams described in the article, we can identify several common patterns:

- Exploiting urgency and fear: All three scam types create a sense of urgency or concern (banking issues, router hacks, time-limited investment opportunities) to pressure victims into acting quickly without proper verification.
- Authority impersonation: Scammers pose as legitimate entities (banks, tech support, financial professionals) to build credibility and trust.
- Technical deception: They use convincing technical elements, such as official-looking websites, SMS spoofing, and remote access tools, to appear legitimate.
- Psychological manipulation: Scammers build trust over time (especially in investment scams) before requesting financial transactions.
- Digital vulnerability: These scams exploit the convenience of digital banking and online transactions, where face-to-face verification is absent.
Comprehensive Prevention Strategies
Individual-level Protection
- Verify independently:
- Never call numbers provided in suspicious messages
- Look up official contact information separately
- Call your bank directly using the number on your card
- Implement technical safeguards:
- Enable multi-factor authentication on all accounts
- Set up transaction notifications for all amounts
- Use bank apps instead of following links
- Set reasonable transaction limits that match your spending patterns
- Practice critical skepticism:
- Be suspicious of unexpected contacts about financial matters
- Question urgent requests for information or money
- Be wary of grammatical errors or generic greetings
- Remember that legitimate institutions never ask for passwords or OTPs
- Follow the “pause principle”:
- Take time before responding to urgent-seeming requests
- Consult with trusted friends or family before large transactions
- Research investment opportunities thoroughly before committing

Red Flags to Watch For
- Unsolicited communications about financial or technical issues
- Requests for remote access to your devices
- Promises of unusually high investment returns
- Pressure to act immediately
- Requests for personal financial information or passwords
- Instructions to transfer money to overseas accounts
- Threats of legal consequences if you don’t comply

By understanding these patterns and implementing these preventive measures, individuals can significantly reduce their vulnerability to common scams. The most effective defense combines technical safeguards with heightened awareness and a healthy skepticism toward unexpected financial communications.
Analysis of Singapore’s Scam Prevention Approach
Government and Institutional Measures
Based on the article, Singapore has implemented several institutional approaches to combat scams:
- Monetary Authority of Singapore (MAS) Initiatives:
- Working directly with banks to enhance digital banking security
- Implementing new protective measures like eliminating clickable links in official emails/SMSes
- Requiring a minimum 12-hour delay before activating new soft tokens on mobile devices
- Providing specific guidance to banking customers on safe practices
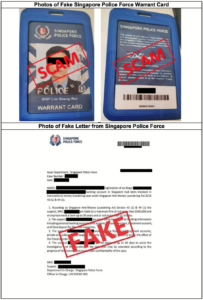
- Police Force Involvement:
- The Singapore Police Force (SPF) actively tracks and reports on scam statistics
- Conducts investigations of scammers and money mules (as evidenced by the case involving 170 men and 89 women)
- Shares examples and screenshots of scams to raise public awareness
- Banking Sector Protections (specifically highlighted for DBS):
- Stopping non-essential SMSes with links
- Sending only essential communications like security notifications and OTP authentication
- Implementing default transaction notification thresholds (S$100)
- Providing in-app security features like card locking and customizable spending limits
- Offering digital tokens with enhanced encryption

Effectiveness Analysis
The approach appears to be multi-faceted, combining:
- Technical barriers: Implementing security features that make scamming more difficult
- Public education: Raising awareness about standard scam techniques
- Enforcement: Actively investigating scam cases
However, the rising scam statistics mentioned (16% increase in cases, with amounts cheated rising from S$63.5M to S$168M) suggest these measures may be struggling to keep pace with evolving scam techniques.

Strengths of Singapore’s Approach
- Coordinated response: Collaboration between regulatory bodies (MAS), law enforcement (SPF), and financial institutions
- Customer-focused solutions: Tools that give customers more control over their security
- Practical implementation: Specific, actionable measures rather than just general advice

Potential Gaps and Recommendations
- Technology gap: The article doesn’t mention advanced detection technologies like AI for identifying unusual transaction patterns
- Demographic considerations: No specific mention of tailored approaches for vulnerable groups like seniors
- Private sector cooperation: Limited discussion of how businesses beyond banks are involved in prevention
- International coordination: No mention of cooperation with other countries to address overseas-based scammers
Singapore’s approach appears to be comprehensive but could potentially benefit from more advanced technological solutions and broader cooperation across sectors and borders to address the evolving nature of scams.
Social Engineering: Anatomy of Manipulation and Defense
Social Engineering Techniques
Psychological Manipulation Strategies
- Authority Impersonation
- Scammers pose as official representatives (e.g., bank officers, government officials)
- Exploit victims’ respect for authority and tendency to comply with perceived authoritative figures.
- Use official-sounding language, titles, and fabricated credentials.
- Fear and Urgency Tactics
- Create artificial time pressures to prevent critical thinking
- Trigger emotional responses like panic or anxiety
- Common threats include:
- Legal consequences
- Financial penalties
- Account suspension
- Potential criminal investigations

- Trust Building and Rapport
- Develop a seemingly genuine conversational flow
- Use personal details to appear credible
- Gradually escalate requests, starting with minor, seemingly innocuous asks
- Exploit human tendency to be helpful and avoid confrontation

- Information Harvesting
- Collect fragmentary personal information from multiple sources
- Use social media, public databases, and previous data breaches
- Craft highly personalized, convincing narratives
Technical Manipulation Methods
- Phishing Techniques
- Spoofed communication channels
- Lookalike websites and email addresses
- Malicious links and attachments
- Screen sharing and remote access exploitation

- Multi-Stage Scam Progression
- Complex narratives involving multiple fake personas
- Gradual erosion of victim’s skepticism
- Continuous redirection and technical jargon
Prevention Strategies
Personal Awareness and Education

- Critical Thinking Development
- Always verify unsolicited communications independently
- Use official contact methods from verified sources
- Never click links or download attachments from unknown sources
- Recognize and resist emotional manipulation
- Communication Red Flags
- Unsolicited contact requesting personal information
- Pressure to act immediately
- Requests for financial transfers
- Communication via unofficial channels
- Threats or aggressive language

Technical Protective Measures
- Digital Security Practices
- Use multi-factor authentication
- Regularly update software and security systems
- Install reputable antivirus and anti-malware solutions
- Use dedicated communication and banking apps
- Enable transaction notifications

- Information Protection
- Minimize public personal information sharing
- Use privacy settings on social platforms
- Create complex, unique passwords
- Regularly monitor financial statements
- Use virtual credit cards for online transactions
Institutional and Technological Interventions
- Technological Defenses
- Implement AI-driven fraud detection systems
- Develop advanced caller ID and communication verification tools
- Create comprehensive scam reporting mechanisms

- Educational Initiatives
- Regular public awareness campaigns
- School and workplace training programs
- Clear, accessible resources on emerging scam techniques
- Collaborative efforts between government, tech companies, and financial institutions
Psychological Resilience

- Emotional Intelligence
- Recognize personal emotional triggers
- Practice calm, methodical responses to unexpected communications
- Develop healthy skepticism without becoming paranoid
- Community Awareness
- Share scam experiences
- Supporting vulnerable community members
- Create support networks for scam victims
Emerging Trends
- Increasing sophistication of AI in social engineering
- Cross-platform information integration
- More personalized, contextually relevant scam attempts
Conclusion
Social engineering exploits fundamental human psychological vulnerabilities. Comprehensive defense requires a multi-layered approach combining technological solutions, personal awareness, and continuous education.
Maxthon

Maxthon has set out on an ambitious journey aimed at significantly bolstering the security of web applications, fueled by a resolute commitment to safeguarding users and their confidential data. At the heart of this initiative lies a collection of sophisticated encryption protocols, which act as a robust barrier for the information exchanged between individuals and various online services. Every interaction—be it the sharing of passwords or personal information—is protected within these encrypted channels, effectively preventing unauthorised access attempts from intruders.
Maxthon private browser for online privacyThis meticulous emphasis on encryption marks merely the initial phase of Maxthon’s extensive security framework. Acknowledging that cyber threats are constantly evolving, Maxthon adopts a forward-thinking approach to user protection. The browser is engineered to adapt to emerging challenges, incorporating regular updates that promptly address any vulnerabilities that may surface. Users are strongly encouraged to activate automatic updates as part of their cybersecurity regimen, ensuring they can seamlessly take advantage of the latest fixes without any hassle.
In today’s rapidly changing digital environment, Maxthon’s unwavering commitment to ongoing security enhancement signifies not only its responsibility toward users but also its firm dedication to nurturing trust in online engagements. With each new update rolled out, users can navigate the web with peace of mind, assured that their information is continuously safeguarded against ever-emerging threats lurking in cyberspace.
